Technical surveillance countermeasures
In-building monitoring systems that address the threat of state and corporate espionage


TSCM overview
Critical infrastructure, corporations, and government entities are vulnerable to internal threats, competitors seeking to steal secrets, and foreign state-sponsored espionage. RF transmitters used for espionage are discrete, capable, and accessible. Without good operational security and investing in Technical Surveillance Countermeasures to detect and address any threats, undetected RF surveillance and data transmissions can allow an adversary to:
- Conduct ISR operations
- Breach secure communications
- Collect classified information
- Steal intellectual property
- Steal money and financial data
- Compromise intelligence agency operations

Multi-layered TSCM
TSCM, also known as electronic counter-surveillance, detects and neutralizes surveillance devices, including hidden cameras, microphones, and other electronic eavesdropping tools.
The traditional approach to RF security involves using sweep teams; however, sweeps can easily be defeated by using detection-avoiding techniques, including frequency hopping, hiding close to a high-power signal, or transmitting in short, infrequent bursts. Devices can also be deactivated during a sweep and turned on when complete.
Used alone, traditional approaches are now impotent. The most robust strategy against RF surveillance involves a multi-layered approach that carries out continuous, real-time TSCM.
A multi-layered approach involves installing an in-place monitoring system for continuous monitoring of the RF environment, essential for round-the-clock monitoring and immediate detection of security breaches.
RFeye Guard at a glance
Highly sensitive RF receivers
Timing synchronization
indoors
100 MHz IBW wideband
frequency monitoring
9 kHz to 40 GHz sweeps

Gateway to powerful
software & APIs

Easy installation,
setup & operation


RFeye SyncLinc
SyncLinc is typically used where no GPS timing signal is present. It is often used when Nodes are placed indoors when performing TSCM work, such as in RFeye Guard. Synclinc permits time synchronization of multiple RFeye Nodes. The goal is to allow each node to capture data within one sampling clock cycle of another, by distributing an accurate timing reference from a master sensor to a group of slave sensors.
This highly accurate common-timing reference allows advanced correlative operations, including high-accuracy Power On Arrival (POA) geolocation with indoor Nodes, retaining the full performance of the RFeye Node, even for transient and low-power signals.

BROCHURE
Continuous real-time in-building
monitoring for Technical
Surveillance Counter Measures
In an era where the threat of espionage is a real-world concern, protecting sensitive information and ensuring your facility’s security is paramount. RFeye Guard offers continuous, real-time in-building monitoring designed to combat the ever-growing threat of covert surveillance devices.
Talk to an advisor about TSCM

ENSURING RF SPECTRUM SECURITY AT A HIGHLY SECURE FACILITY
How a security service detects and geolocates unwanted signals to safeguard national security
Read the story
Key benefits of a TSCM solution
installed in your facility

- Continuous RF surveillance
- Complete RF security
- Flexible deployment
- Early threat detection
- Broad spectrum coverage
- Geolocation capabilities
- Automation and ease of use
- Central management
- Integrate with other security measures
Frequently asked questions
What is TSCM?
TSCM, or Technical Surveillance Countermeasures, is the process of locating and identifying surveillance devices that may be used to spy on individuals or organizations. TSCM professionals use specialized equipment and techniques to sweep an area for hidden cameras, microphones, tracking devices, and other covert surveillance tools. By conducting regular TSCM sweeps, organizations can protect their privacy and confidential information from potential eavesdropping or data breaches.
Read the deployment story: Ensuring RF spectrum security at a highly secure facility.
TSCM involves a thorough and systematic sweep of an area (inner sanctum, no-mobile designated area, crisis / briefing rooms, data rooms, quantum labs etc) to detect any hidden surveillance devices such as bugs, hidden cameras, or wiretaps. This process typically involves using specialized equipment such as spectrum analyzers and non-linear junction detectors to detect electronic signals and hidden devices.
It almost certainly involves designated in-building zone monitoring as well as immediate external permitter monitoring.
Where is TSCM used?
TSCM, or Technical Surveillance Countermeasures, is used in a variety of settings to protect sensitive information, ensure spectrum superiority, and secure facilities against electronic eavesdropping devices or electronic attack. This includes government buildings, corporate offices, financial institutions, embassies, data centres and quantum labs, for example.
TSCM is also utilized in legal proceedings, private investigations, and during mergers and acquisitions to ensure that confidential information remains secure. In general, TSCM (also known as in-building spectrum monitoring or as a building monitoring system), is employed in any environment where there is a need to safeguard against unauthorized surveillance and protect highly sensitive information from falling into the wrong hands (hostile foreign nation, corporate or private).
Understanding the applications of Technical Surveillance Countermeasures – read the deployment story: Ensuring RF spectrum security at a highly secure facility.
What does TSCM stand for?
TSCM stands for Technical Surveillance Counter Measures. This term refers to the process of detecting, geolocating and mitigating electronic eavesdropping devices, also known as bugs, that may be used to spy on individuals or organizations. TSCM experts use specialized equipment (electronic sweeps as well continuous spectrum building monitoring systems) and techniques to sweep secure, sensitive or no-go cell / mobile zones) for hidden listening, recording or receiver devices and other surveillance equipment.
Basic TSCM involves physical searches and electronic sweeps.
Sophisticated TSCM, of the kind employed in embassies, situation rooms, quantum labs and SCIFs for example, requires continuous spectrum building monitoring systems that perform 24/7/365 sweeps, use detectors, automation and geolocation to guard against unauthorized surveillance, counter espionage and cyber-attack threats.
Why conduct a TSCM sweep?
Conducting a Technical Surveillance Counter Measures (TSCM) sweep is essential to safeguarding sensitive information and protecting against unauthorized surveillance activities.
By proactively searching for and identifying any hidden microphones, RF receivers or other spying devices, individuals and organizations can prevent potential security breaches, data leaks, and privacy violations. TSCM sweeps help ensure that confidential conversations remain confidential, trade secrets are not compromised, and intellectual property remains secure.
Here are some reasons why conducting a TSCM sweep is crucial:
- Protecting sensitive information: In today's digital age, it is easier than ever for individuals or organizations to use surveillance devices to gather sensitive information. By conducting a TSCM sweep, you can ensure that your confidential information remains secure and protected from unauthorized access.
- Maintaining privacy: Privacy is a fundamental right that should be respected and protected. Conducting a TSCM sweep can help you maintain your privacy and prevent unwanted surveillance.
- Preventing corporate espionage: Businesses and organizations are often targeted by competitors, hostile foreign nations, or malicious actors who seek to gain an advantage through espionage. Conducting a TSCM sweep can help you detect, geolocate and remove any surveillance devices that may have been planted to gather sensitive business information.
- Ensuring peace of mind: Knowing that your facility is protected and secure against surveillance devices can provide you with peace of mind and allow you to go about your daily activities without risk – operational, human capital or IP.
- Compliance with regulations: In some industries, such as government agencies or financial institutions, conducting regular TSCM sweeps may be required to comply with regulations and ensure the security of sensitive information.
- Intellectual property: TSCM sweeps are routine and integral to preserving IP in commercial and defense facilities for example.
- National security: TSCM sweeps of the kind enables by CRFSs RFeye Guard for example, are part of the continuous spectrum building monitoring systems employed by governments and corporate organizations focused on national security, defense, cyber and intelligence services.
In conclusion, conducting a TSCM sweep is crucial for protecting sensitive information, maintaining privacy, preventing corporate espionage, ensuring peace of mind, and complying with regulations. By investing in TSCM services, you can safeguard your facility from unauthorized surveillance and maintain the security of your confidential information.
What is a building monitoring system?
A building monitoring system is a network of sensors and devices that are installed in a building to monitor and control various aspects of its operations. These systems are designed to collect data on factors such as security and cyber-attack, temperature, humidity, air quality, energy usage, for example.
TSCM or Technical Surveillance Countermeasures focus on mitigating the threat of counter surveillance, espionage, cyber-attack, and unauthorized listening or spying.
By providing real-time spectrum monitoring and analysis, a sophisticated TSCM building monitoring system can provide 24/7/365 security from rouge employees, foreign nation espionage and malicious corporate hacking.
Discover hardware
CRFS offers a combination of fixed, tactical, and mobile hardware solutions, which can be used as versatile, re-deployable systems that do not require recalibration.

RFeye Guard
Receiver technology detecting low-power signals. The system combines highly sensitive and broad bandwidth receivers with simple autonomous software to ensure you never miss an illicit signal.

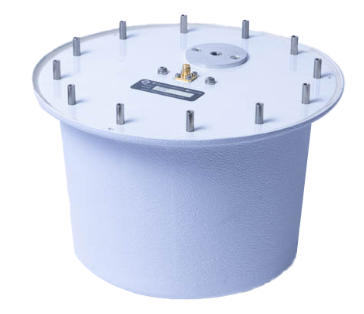
RFeye Node 100-18
The wideband RFeye Node 100-18 is a complete spectrum monitoring and geolocation system. Optimized for size, weight, and power (SWaP), it is simple to connect, power, and network.
Get instant news & expert insights
Join thousands of professionals who subscribe for exclusive insights and early access to our reports and analysis.
