Solutions for security & intelligence agencies
Actionable RF intelligence and counter surveillance solutions to fight crime and address homeland security threats
Overview
Security, law enforcement, and intelligence agencies need a range of tools to capture RF data, geolocate signals, and locate jamming equipment. They can also benefit from capturing I/Q and spectrum data over long periods to establish patterns of life, create baselines, and conduct signal analysis and decoding.
The RFeye ecosystem is a highly versatile and reliable hardware and software platform, providing essential solutions for real-time spectrum monitoring, covert surveillance, counter-surveillance, geolocation, and jamming detection. It gives agencies the ability to detect, monitor, analyze, and act upon a vast range of wireless signals—providing a significant advantage in terms of situational awareness, investigative capabilities, and proactive threat response.
Spectrum monitoring & counterintelligence
Critical infrastructure protection
Long-term capture of I/Q & spectrum data
Detect PTT, jammers, & illicit activity
- Support covert surveillance
Geolocating suspect transmitters
TSCM in-building threat management
Key benefits
-
Outstanding RF performance & sensitivity
High-performance passive RF sensors can monitor a wide range of frequencies and differentiate between legitimate and suspicious signals. Operators can respond in real-time to locate, listen to, and decode transmissions.
-
Optimized for size, weight, & power (SWaP)
CRFS’ RF receivers have been optimized for SWaP, and can be easily integrated into covert spaces. They have optimized power efficiency, decreased chances of failure due to thermal stress, and enhanced reliability and durability.
-
Configure missions with headless operation
Headless operation allows operatives to configure missions in advance—either remotely or directly through the RF receiver, which passively collects data autonomously.
-
Record terabytes of data for offline storage
Recording huge amounts of signal data over time allows operatives to conduct post-analysis, which helps organizations refine their security strategies based on observed patterns.
-
Collect data to support prosecution
Timestamped spectrum data can establish timelines that can be crucial for establishing culpability or corroborating other evidence. Forensic analysis of high-fidelity RF captured data can unlock vital intelligence and support law enforcement and homeland security.
-
Support the intelligence ecosystem with a wide range of data formats
CRFS’ RF receivers support a wide range of data formats to satisfy the diverse requirements of the intelligence ecosystem, ensuring compatibility and seamless integration with various analysis, storage, and communication systems used around the world.
Outstanding RF performance & sensitivity
High-performance passive RF sensors can monitor a wide range of frequencies and differentiate between legitimate and suspicious signals. Operators can respond in real-time to locate, listen to, and decode transmissions.
Optimized for size, weight, & power (SWaP)
CRFS’ RF receivers have been optimized for SWaP, and can be easily integrated into covert spaces. They have optimized power efficiency, decreased chances of failure due to thermal stress, and enhanced reliability and durability.
Configure missions with headless operation
Headless operation allows operatives to configure missions in advance—either remotely or directly through the RF receiver, which passively collects data autonomously.
Record terabytes of data for offline storage
Recording huge amounts of signal data over time allows operatives to conduct post-analysis, which helps organizations refine their security strategies based on observed patterns.
Collect data to support prosecution
Timestamped spectrum data can establish timelines that can be crucial for establishing culpability or corroborating other evidence. Forensic analysis of high-fidelity RF captured data can unlock vital intelligence and support law enforcement and homeland security.
Support the intelligence ecosystem with a wide range of data formats
CRFS’ RF receivers support a wide range of data formats to satisfy the diverse requirements of the intelligence ecosystem, ensuring compatibility and seamless integration with various analysis, storage, and communication systems used around the world.
Discuss an RF monitoring or counterintelligence requirement with an advisor





DETECTION & 3D GEOLOCATION OF AERIAL TARGETS OVER WIDE AREAS
How a NATO partner built an air defense platform to increase national security
Read the storyISR MISSIONS AT SEA & ACROSS HOSTILE BORDERS
How combining ground & air-based RF sensors improved ISR and target acquisition.
Read the storyREAL-TIME I/Q DATA CAPTURE FOR ENHANCED INTELLIGENCE
How a national force secured its borders with reliable spectrum data.
Read the storyINCREASING LINE OF SIGHT & GEOLOCATING GROUND-BASED TARGETS FROM A LONG DISTANCE
How TEKEVER & CRFS collaborated to fit UAS with ultra-sensitive RF receivers as a payload.
Read the storyREAL-TIME I/Q DATA CAPTURE FOR ENHANCED INTELLIGENCE
How a national force secured its borders with reliable spectrum data.
Read the story
WHITE PAPER
Angle of arrival / direction finding techniques
Angle of Arrival (AoA) or Direction Finding (DF) techniques are perhaps the most widely-used ways to geolocate radio frequency signals. In this white paper, we outline the various forms of AoA , including how they work, how they can be applied in practice, and how they can be combined with other geolocation techniques such as time difference of arrival (TDoA).
Hardware

RFeye Guard
Receiver technology detecting low-power signals. The system combines highly sensitive and broad bandwidth receivers with simple autonomous software to ensure you never miss an illicit signal.

RFeye Stormcase
Man-portable spectrum monitoring (deploy and retrieve later). The system includes a Node (receive and record), internal and external antenna ports, a high-performance rechargeable MIL-SPEC battery, and integrated SSD memory.

RFeye SenS Portable
The RFeye SenS Portable is a lightweight, portable I/Q recorder for high-fidelity, long-duration RF recording, and signal extraction.

RFeye Node 100-18
The wideband RFeye Node 100-18 is a complete spectrum monitoring and geolocation system. Optimized for size, weight, and power (SWaP), it is simple to connect, power, and network.
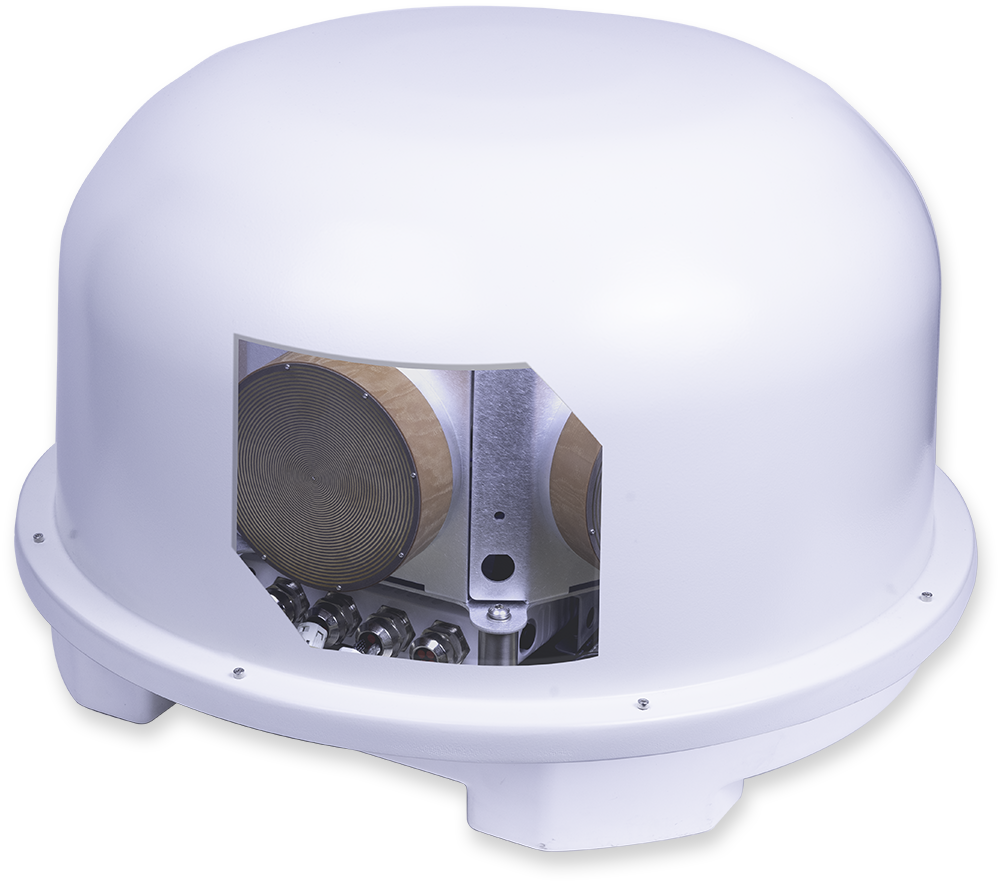
RFeye Array 100
Direction finding and advanced plug-and-play geolocation system. Fully integrated, multi-mission systems for fixed, vehicle, or transportable applications with DF, monitoring, and geolocation capability.
Software
A comprehensive software suite to monitor, capture, analyze, geolocate, and report signals of interest. Our solutions provide teams with a complimentary toolkit for complete spectrum visibility.

RFeye Site
RFeye Site is a toolbox to monitor the spectrum in real-time and geolocate signals in complex RF environments.
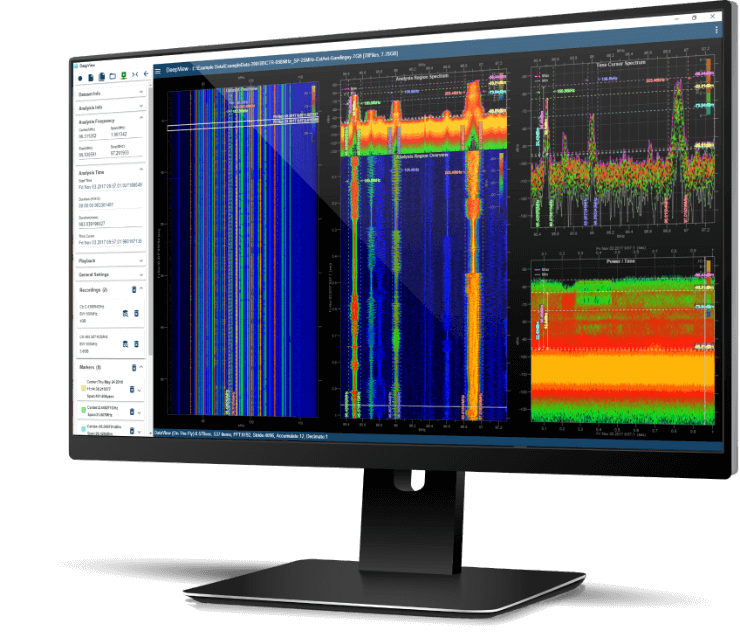
RFeye DeepView
RFeye DeepView is a forensic signal analysis software solution offering a 100% probability of intercept.

Book a callback with an advisor
Let’s talk RF spectrum security and how to detect and geolocate unwanted signals.

